CVE-2026-8438 affects All-In-One Security (AIOS) – Security and Firewall and it is an unauthenticated stored cross site scripting vulnerability in the debug log workflow. When debug mode and the REST API restriction for non-logged in users are enabled, an attacker can place HTML or JavaScript in the REST request path. The decoded path is written into the debug log and later rendered without escaping in the AIOS Dashboard Debug logs page. A single request can therefore plant script that runs in an administrator browser session when the log view is opened, which can lead to nonce theft, privileged actions, and full site compromise.
How Security by CleanTalk Password Leak Check Stops a Weak WordPress Admin Password
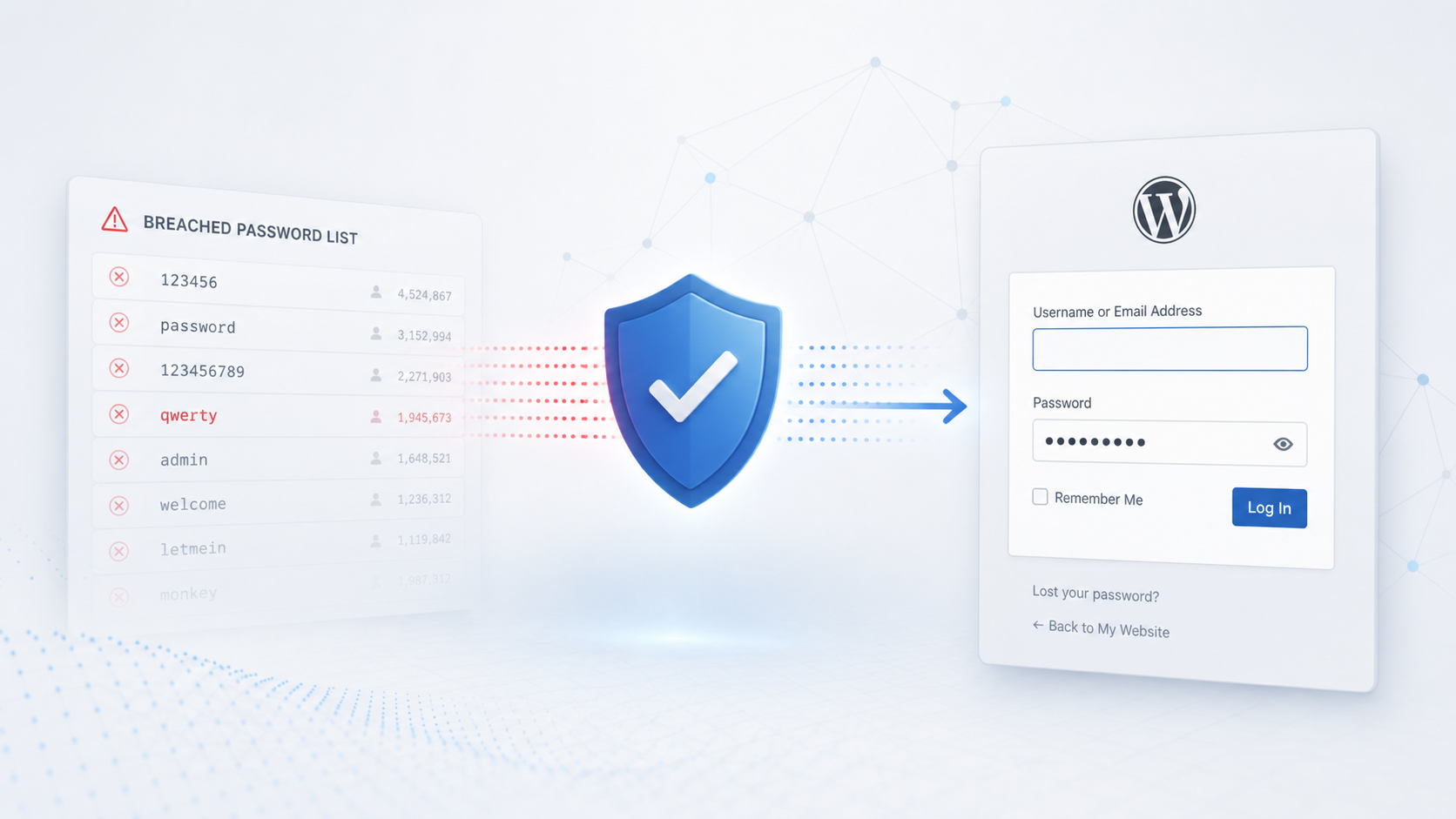
A practical review of Security by CleanTalk Password Leak Check using a test WordPress administrator with the exposed password qwerty. The feature detected the leaked credential, marked the account as risky, and forced password replacement before the administrator could continue working in wp-admin.
How Security by CleanTalk Protects WordPress Websites with Signature Analysis and Cloud Malware Detection

Every day, thousands of WordPress websites become targets for cybercriminals. Vulnerable plugins, outdated themes, weak passwords, and newly discovered security flaws allow attackers to upload malicious code, web shells, SEO spam, backdoors, and other dangerous files.
In many cases, website owners are completely unaware that their site has been compromised. Malware can remain active for weeks or even months while secretly redirecting visitors, sending spam, creating hidden administrator accounts, or providing attackers with full control over the server.
CVE-2026-0722 – Shield Security – CSRF to SQLi – POC

CVE-2026-0722 affects Shield Security and covers a CSRF bypass that can be chained into SQL injection in versions up to and including 21.0.8. The vulnerable AJAX flow can be reached through wp-admin/admin-ajax.php with action=shield_action and ex=traffictable_action, where a forged request can disable nonce verification through action_overrides[is_nonce_verify_required]=0.
CVE-2026-0561 – Shield Security – Unauth Reflected XSS – POC

CVE-2026-0561 affects Shield Security and describes an unauthenticated reflected Cross-Site Scripting issue in versions up to and including 21.0.8. The vulnerable dynamic page renderer accepts the message parameter on the shield_action flow and reflects it into a generated page without sufficient sanitization and output escaping. An attacker does not need a WordPress account. They only need to persuade a victim to open a crafted URL, which can make script run in the victim browser under the site origin. For logged in administrators, that can expose WordPress nonces and allow authenticated browser actions through the victim session.
CVE-2026-7660 – Easy Updates Manager – Reflected XSS – POC

CVE-2026-7660 affects Easy Updates Manager in versions up to 9.0.20 and it is a reflected Cross Site Scripting issue in the admin pagination flow. The vulnerable path is the Updates Options plugins tab, where the paged request parameter can be reflected into the value attribute of the current page input when action=eum_ajax is present. A successful attack requires an administrator or another user with update management access to open a crafted admin URL, so the practical risk is a privileged reflected script sink that can execute in the WordPress dashboard if the browser accepts the injected attribute payload.
CVE-2026-9284 – WooCommerce PayPal Payments – Missing Authorization – POC

CVE-2026-9284 affects WooCommerce PayPal Payments and it is a missing authorization issue in the subscription approval checkout flow. In vulnerable builds up to 4.0.1, a public WC-AJAX request can place a client supplied PayPal subscription identifier into the WooCommerce session, and the subscriptions integration can later treat that session value as enough evidence to complete a WooCommerce order. On stores that use WooCommerce Subscriptions with PayPal subscription checkout, this can let an unauthenticated visitor move an order to a paid state without a successful PayPal capture or approval, which creates direct financial risk and unreliable payment records.
Plugin Security Certification (PSC-2026-64664): “Kadence Blocks — Page Builder Toolkit for Gutenberg Editor” – Version 4.1.9

Kadence Blocks is a powerful extension for the native WordPress block editor, designed to provide advanced Gutenberg blocks, responsive layout controls, dynamic design tools, and professional website-building functionality without requiring custom code.
The plugin extends WordPress with a wide collection of custom blocks including Accordions, Advanced Buttons, Forms, Galleries, Tabs, Testimonials, Post Grids, Row Layouts, Progress Bars, Lottie Animations, and many more. It is optimized for performance, accessibility, and scalability while maintaining clean frontend output and modern design standards.
Plugin Security Certification (PSC-2026-64661): “Enable Media Replace” – Version 4.1.9

Media replacement plugins work directly with the WordPress upload directory, attachment records, file names, MIME types, and references embedded across posts and pages. That makes them operationally useful, but also security-sensitive: insufficient checks can lead to arbitrary file upload, unauthorized file overwrite, path manipulation, or integrity damage to existing content. Enable Media Replace version 4.1.9 has successfully completed the CleanTalk Plugin Security Certification process and received PSC-2026-64661, confirming that the plugin was reviewed from a secure code perspective with attention to common exploitation paths for media management and file replacement plugins.
Plugin Security Certification (PSC-2026-64662): “Instant Images – One-click Image Uploads from Unsplash, Openverse, Pixabay, Pexels, and Giphy” – Version 7.1.1

Image import plugins bridge WordPress with external media providers, proxy services, remote image URLs, metadata processing, and the local Media Library. That workflow improves publishing speed, but it also expands the attack surface around remote downloads, MIME validation, alt text and caption handling, attribution metadata, and editor integrations. Instant Images version 7.1.1 has successfully completed the CleanTalk Plugin Security Certification process and received PSC-2026-64662, confirming that the plugin was reviewed from a secure code perspective with attention to common exploitation paths for remote image import and media-library workflow plugins.